Enterprise Key Management (EKM) for Volt Foundry
Overview
Enterprise Key Management (EKM) in Volt Foundry provides a secure, centralized way to manage and use credentials across Foundry services.
Administrators create and manage credentials in an encrypted keystore. Developers select preconfigured credential IDs when configuring services, without accessing the actual secret values.
Key Capabilities
-
Admin-only credential management: Only Admin or Owner users can create, update, delete, and manage credentials in the EKM keystore.
-
Credential abstraction for developers: Developers reference credential IDs instead of actual secret values when configuring services.
-
Encrypted storage: All credential values are stored in encrypted form in the Foundry database. Sensitive fields are never exposed in plaintext.
-
Credential masking: Secret fields (passwords, client secrets, access keys) are masked in all API responses and console views.
-
Ownership control: Credential owners can restrict update permissions to themselves, preventing other admins from modifying their credentials.
-
Multiple credential types: Supports multiple credential types for different Foundry service adapters.
-
Deleted credential detection: Services configured with deleted credentials are clearly flagged in the console to prevent silent failures.
Supported Channels
- On-Premises
- Cloud
Access Control
EKM enforces role-based access control at the account level.
| Role | Manage Credentials | Use Credentials in Services |
|---|---|---|
| Owner | Yes | Yes |
| Admin | Yes | Yes |
| Member/Developer | No | Yes (select credential IDs only) |
Note: Only users with Admin or Owner role can access the EKM settings page to create, edit, delete, or change ownership of credentials. Developers can only select available credential IDs in service configurations.
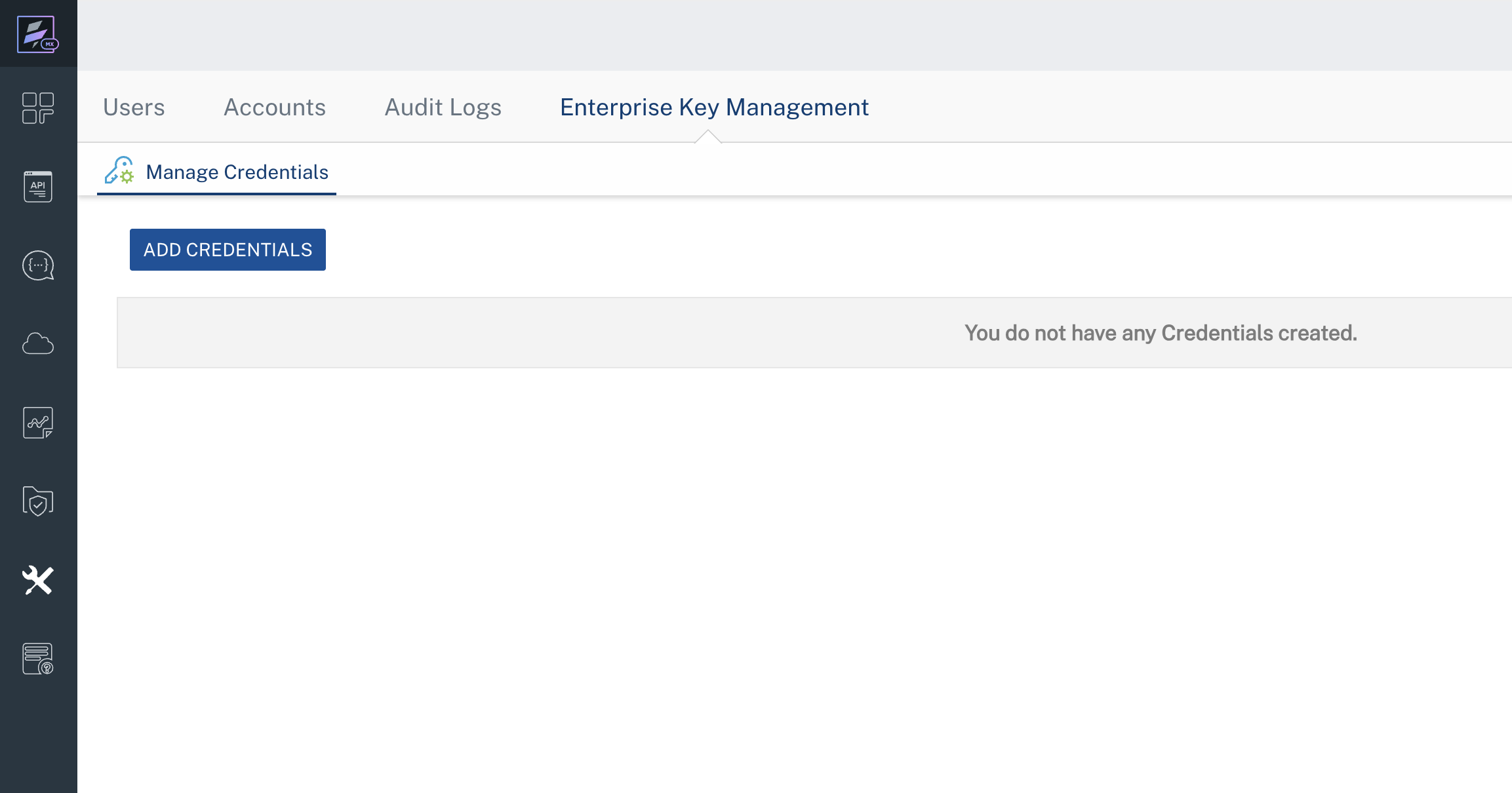
Accessing EKM
To access EKM:
- Log in to the Volt Foundry Console.
- In the left sidebar, click Settings.
- Click Enterprise Key Management.
The Manage Credentials tab appears.
Managing Credentials
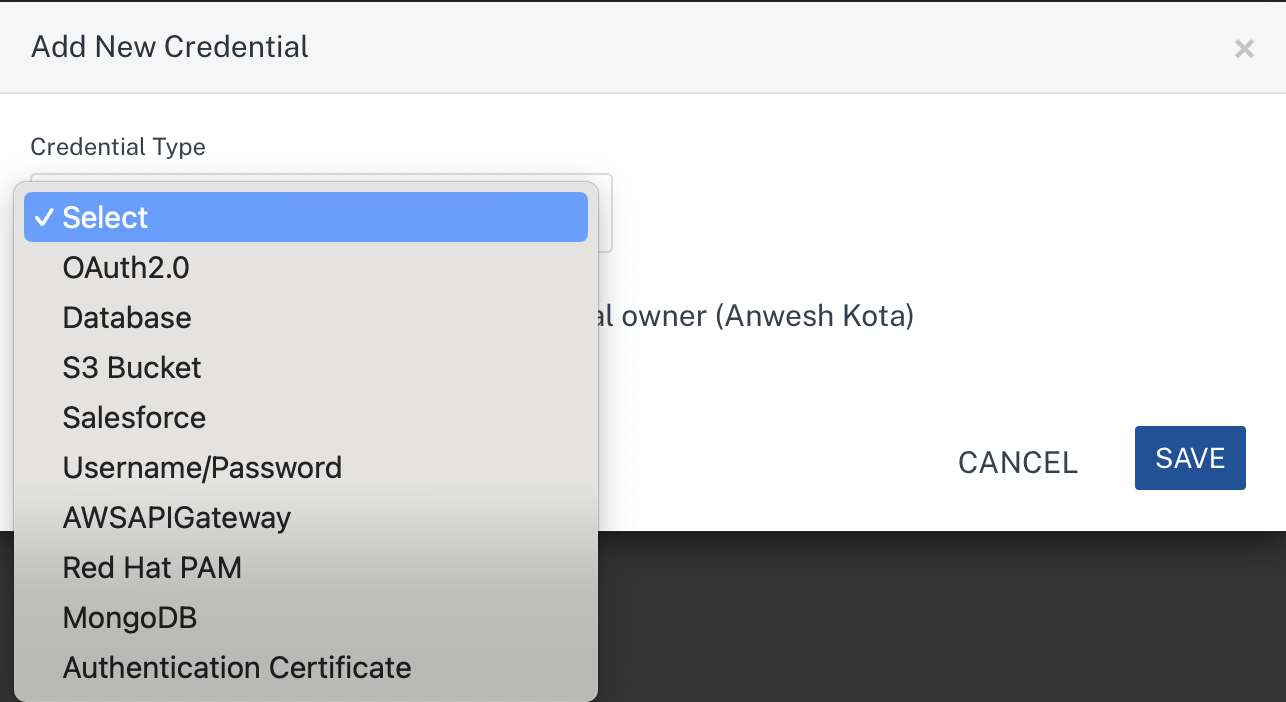
Supported Credential Types
EKM supports the following credential types:
| Credential Type | Fields | Used By |
|---|---|---|
| OAuth2.0 | Client ID, Client Secret | Identity Services (OAuth2 providers) |
| Database | JDBC URL, User ID, Password | Relational Database adapters |
| S3 Bucket | Access Key, Access Secret, Backend URL, Region, Bucket Path, Service Namespace | AWS S3, Cloudian adapters |
| Salesforce | Login URL, Client ID, Client Secret, Username, Password | Salesforce adapters |
| Username/Password | User ID, Password | XML, SOAP, JSON, API Proxy, Text adapters (Basic/NTLM auth) |
| AWSAPIGateway | Access Key ID, Secret Key | AWS API Gateway adapter |
| Red Hat PAM | Endpoint URL, Username, Password | Red Hat PAM adapter |
| MongoDB | Host, Port, Database Name, Username, Password | MongoDB adapter |
| Authentication Certificate | Varies by storage type (see below) | OAuth2 Identity with Certificate-Based Authentication |
Authentication Certificate Sub-Types
The Authentication Certificate credential type supports two storage modes:
| Storage Type | Fields |
|---|---|
| Azure Key Vault | Azure Key Vault URI, Authentication Method (Client Secret or Certificate), Thumbprint, Key Name, Key Version (Optional), API Version, Microsoft Entra Tenant ID, OAuth 2.0 Client ID, JWT Signing Client ID, and Client Secret or Certificate file |
| Foundry Managed | OAuth 2.0 Client ID, Private Key file (.pem/.pfx/.p12) |
Creating a Credential
Before you begin
- Ensure that you have Admin or Owner permissions.
To create a credential:
- Go to Settings > Enterprise Key Management.
-
Click Add Credentials.
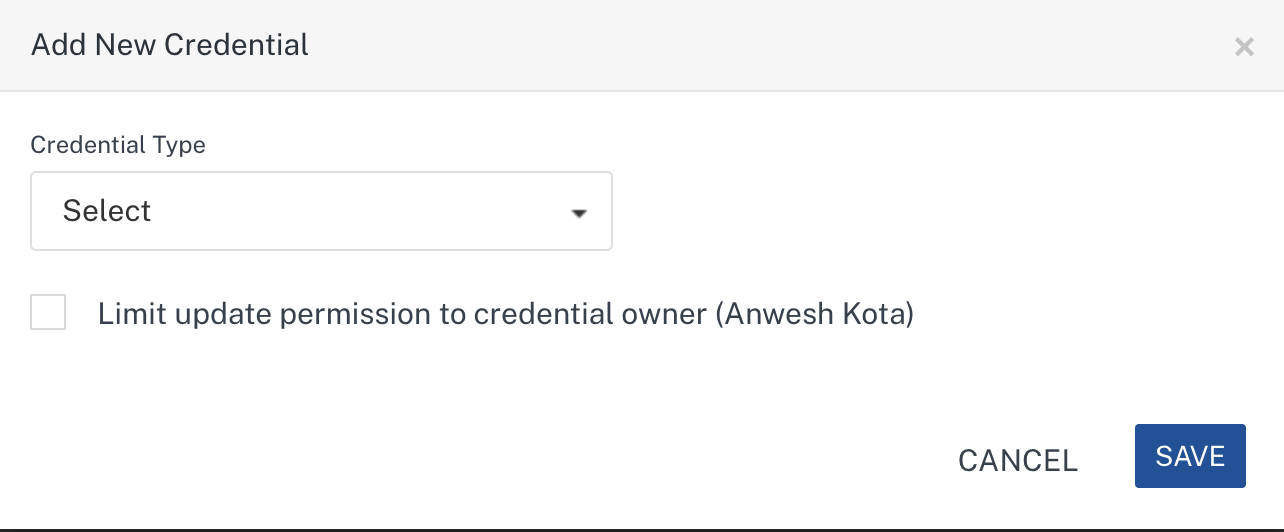
-
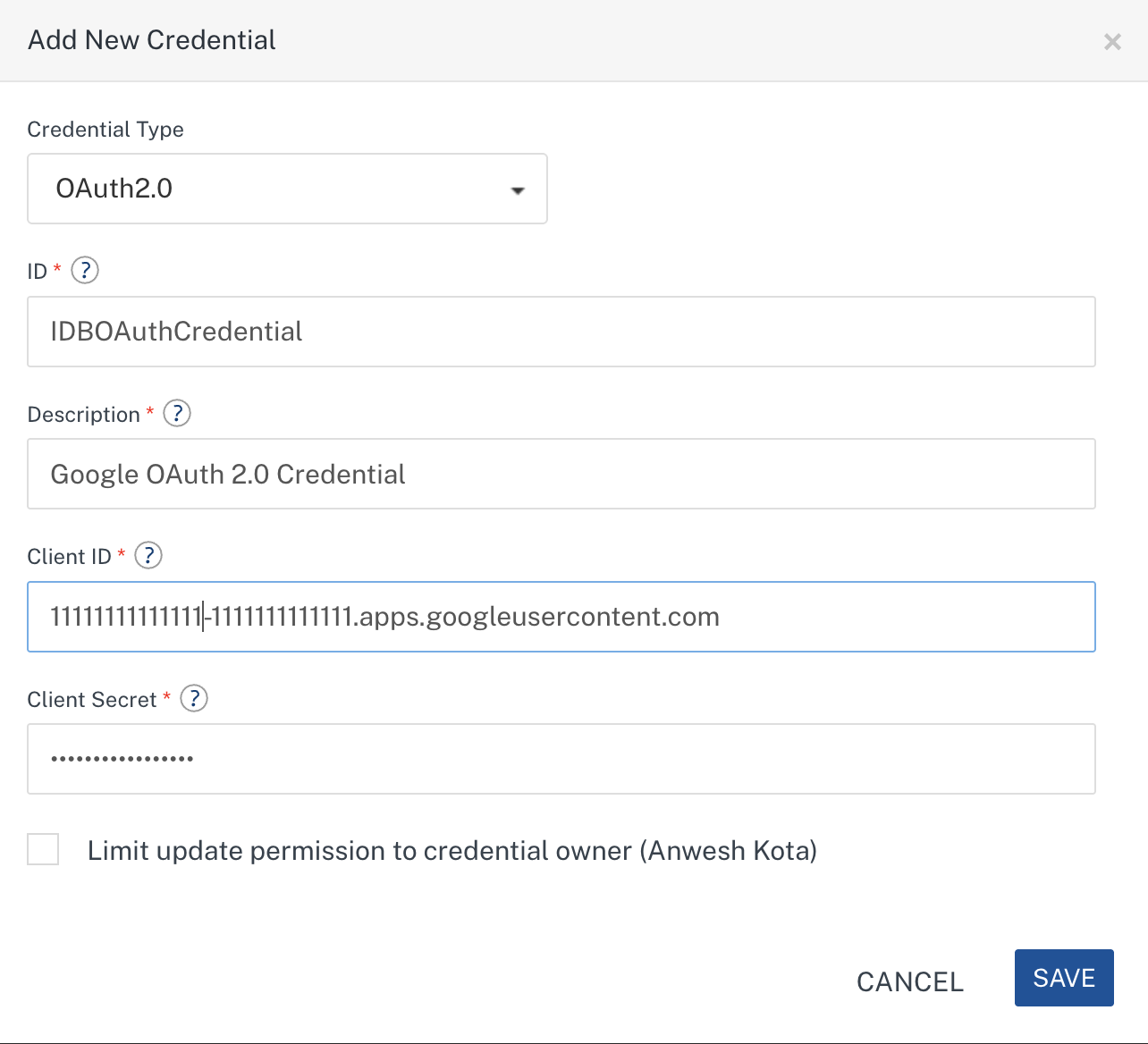
In the Add New Credential dialog, select a Credential Type from the dropdown.
-
Fill in the required fields based on the selected credential type:
- ID: A unique identifier for the credential (used by developers to reference it in services).
- Description: A brief description of the credential.
- Type-specific fields (e.g., Client ID, Client Secret for OAuth2.0).
-
Optionally, select Limit update permission to credential owner to restrict editing to the creator of this credential.
-
Click Save.
Note: For Database credential type, the JDBC URL is validated for connectivity before the credential is saved. If the URL is not valid, an error is displayed.
Note: For Authentication Certificate type, you can upload
.pem,.pfx, or.p12certificate files. Maximum file size is 1 MB.
Editing a Credential
- Go to Settings > Enterprise Key Management.
- Locate the credential in the credentials list.
-
Click the gear icon (⚙) on the credential row and select Edit.
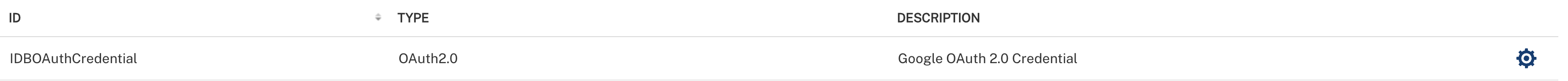
-
Modify the desired fields in the Edit Credential dialog.
Note: The Credential Type and ID cannot be changed after creation.
Note: Sensitive fields (passwords, secrets) are displayed as
****. If you leave a masked field unchanged, the existing value is preserved. -
Click Save.
Deleting a Credential
- Go to Settings > Enterprise Key Management.
- Locate the credential in the credentials list.
- Click the gear icon (⚙) on the credential row and select Delete.
-
A confirmation dialog appears:
"Are you sure you want to delete? If this credential is used in a service, it might stop functioning."
-
Click Delete to confirm.
Important: Deleting a credential that is currently referenced by a service will cause that service to display the credential as [DELETED] in red. You must update the affected services to use a different credential before publishing.
Changing Credential Ownership
- Go to Settings > Enterprise Key Management.
- Locate the credential in the credentials list.
- Click the gear icon (⚙) on the credential row and select Change Ownership.
-
Enter the email ID of the new owner.
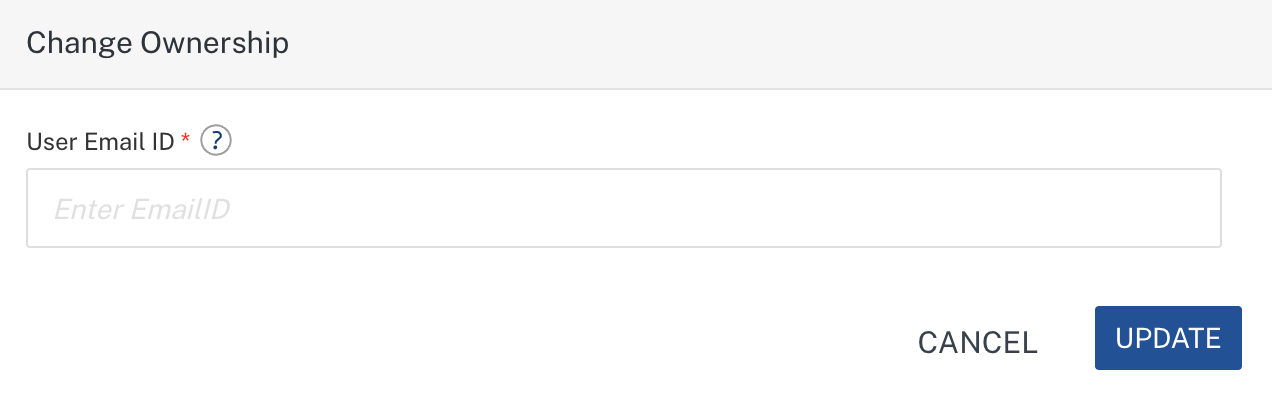
-
Click Update.
Note: The new owner must be an Admin or Owner user on the account. Ownership transfer to Members or Developers is not allowed.
Using EKM Credentials in Services
Developers can reference EKM credentials when configuring Identity, Integration, and Object services. Instead of entering sensitive values directly, developers select a preconfigured credential ID from a dropdown.
Identity Services (OAuth2.0)
EKM credentials can be used in OAuth2 identity providers (e.g., Okta, Google, Microsoft, Facebook, LinkedIn, Amazon, Yahoo, Instagram, Box).
- Go to your app > Identity > select or create an OAuth2 provider.
-
Use credentials from Enterprise Key Management checkbox is auto selected if corresponding credential exists in Enterprise Key Management. If credential doesn't exist it will be unselected.
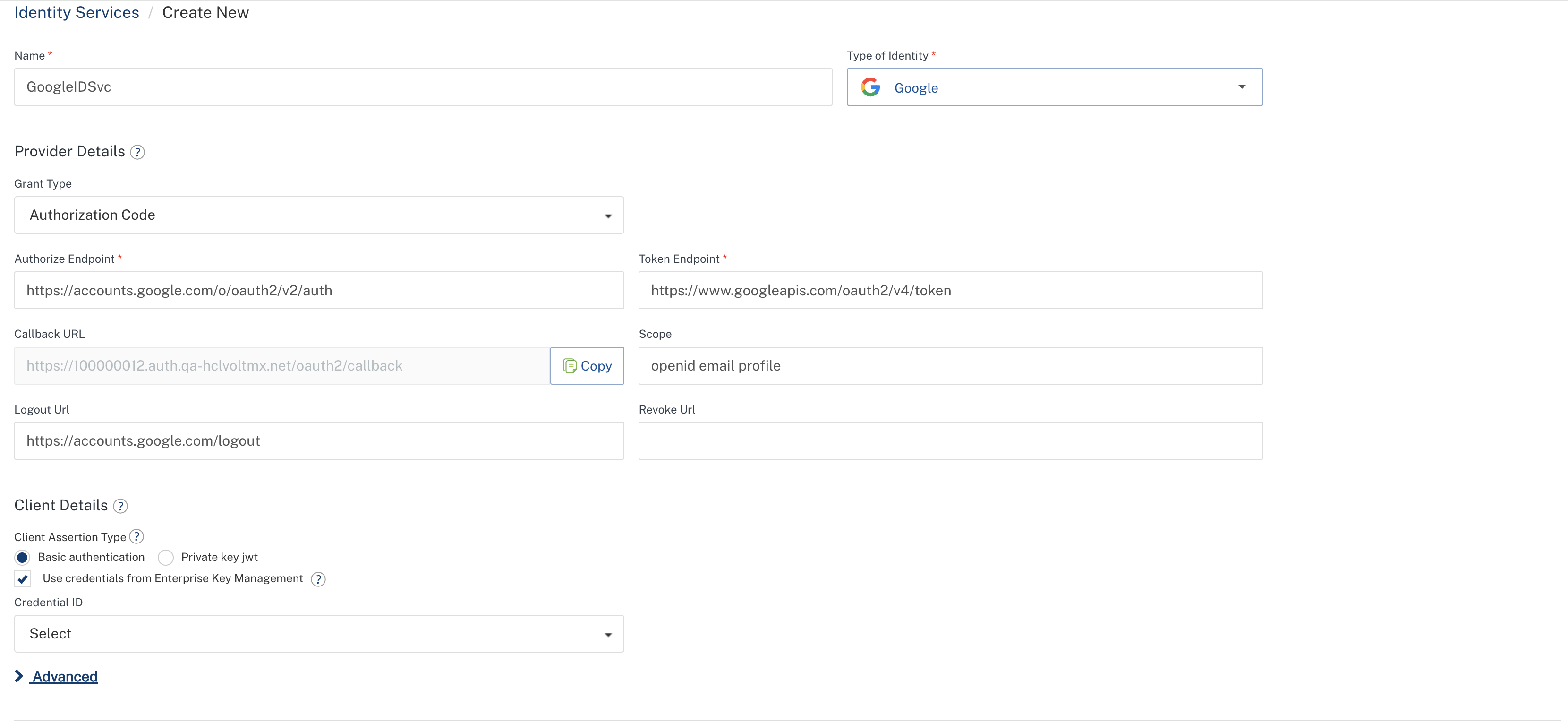
-
A Credential ID dropdown appears. Select the appropriate credential ID.
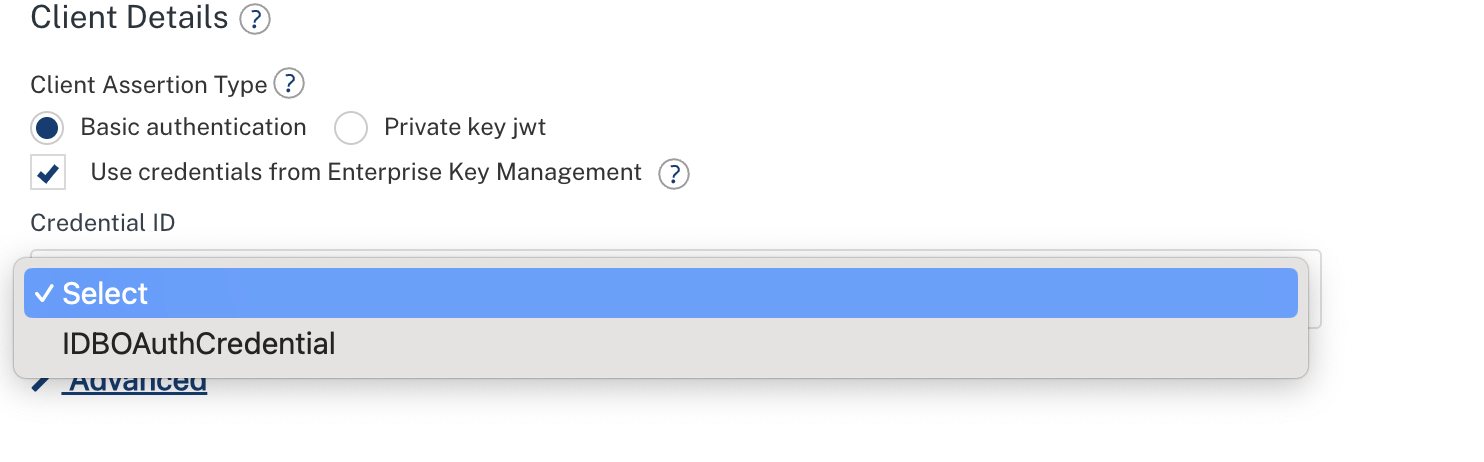
-
When EKM is enabled, the Client ID and Client Secret fields are hidden — these values are automatically resolved from the selected EKM credential.
- Save the identity provider configuration.
Note: The Test Login functionality works with EKM credentials. When testing, the credential values are resolved securely before authenticating with the provider.
Integration Services
EKM credentials can be used with the following integration service adapters:
Technology Adapters:
- XML, SOAP, JSON, API Proxy, Text: Use Username/Password credentials for Basic or NTLM authentication.
Business Adapters:
- AWS API Gateway: Use AWSAPIGateway credentials.
- Salesforce: Use Salesforce credentials.
- Relational Database: Use Database credentials.
- MongoDB: Use MongoDB credentials.
- AWS S3, Cloudian: Use S3 Bucket credentials.
- Red Hat PAM: Use Red Hat PAM credentials.
Steps to Configure
- Go to your app > Integration > select or create a service.
- In the service configuration, locate the authentication section (for technology adapters) or the connection parameters section (for business adapters).
-
Use credentials from Enterprise Key Management checkbox is auto selected if corresponding credential exists in Enterprise Key Management.
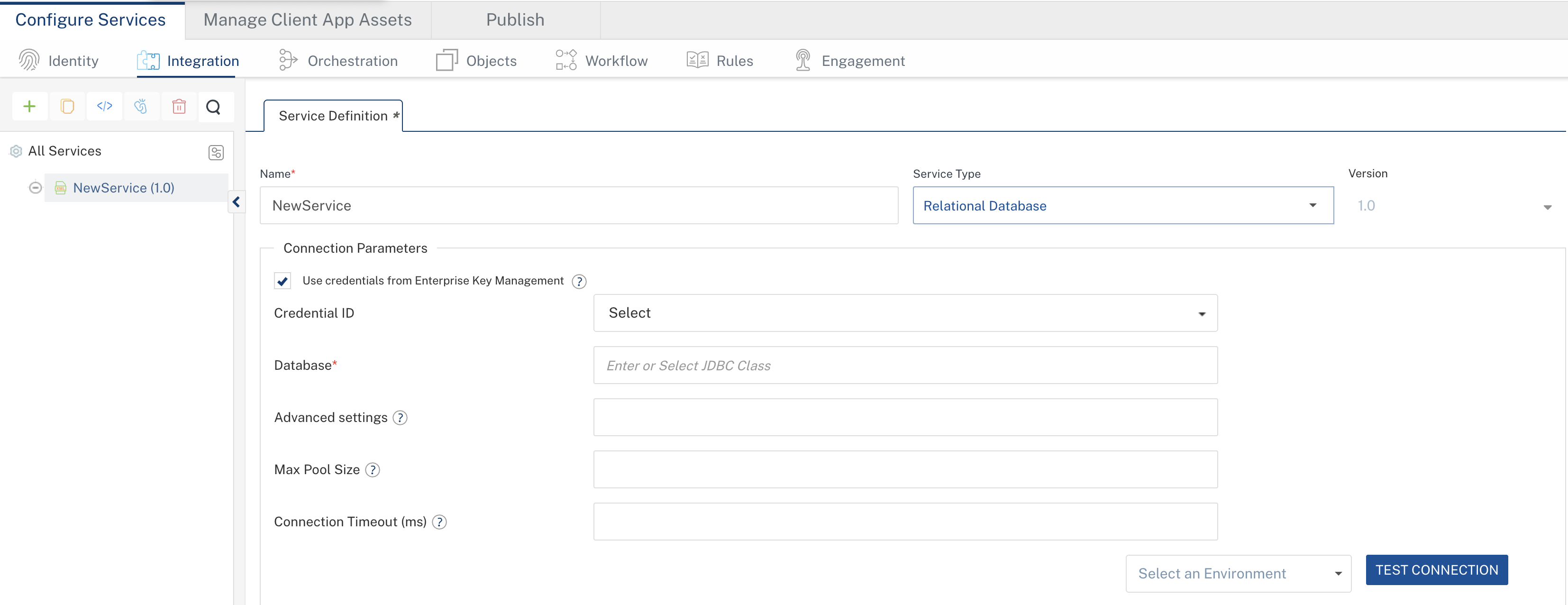
-
A Credential ID dropdown appears. Select the appropriate credential ID.
-
The individual credential fields (User ID, Password, Access Key, etc.) are hidden — values are resolved from the selected EKM credential.
- Save the service configuration.
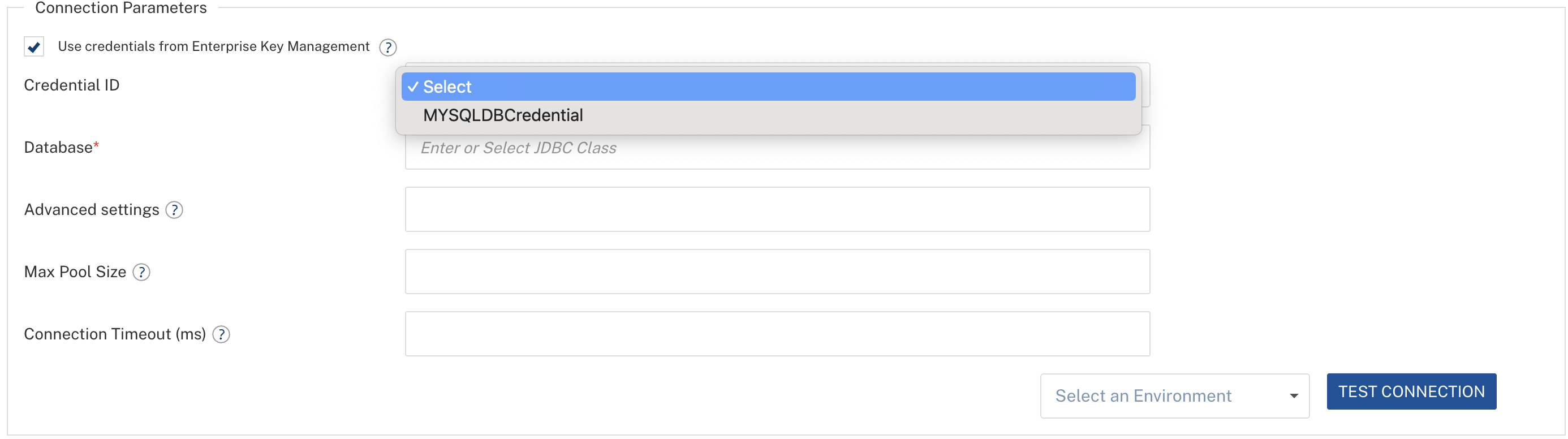
Object Services
EKM credentials can be used with the following Object service adapters:
- Salesforce: Use Salesforce credentials.
- Relational Database: Use Database credentials.
- MongoDB: Use MongoDB credentials.
- AWS S3, Cloudian: Use S3 Bucket credentials.
Steps to Configure
- Go to your app > Objects > select or create an Object service.
-
Use credentials from Enterprise Key Management checkbox is auto selected if corresponding credential exists in Enterprise Key Management.
-
Select the Credential ID from the dropdown.
- Save the endpoint configuration.
Credential Resolution During App Publish
When an application is published to a runtime environment, all EKM credential placeholders in the service configurations are automatically resolved to their actual secret values. This resolution happens securely during the publish process:
- At design time, service configurations reference only credential IDs — no actual secrets are stored in app configurations.
- At publish time, credential IDs are resolved to actual values and securely embedded into the published application artifacts.
- At runtime, the middleware operates with the resolved actual credentials.
Note: Developers never see or handle the actual credential values at any point.
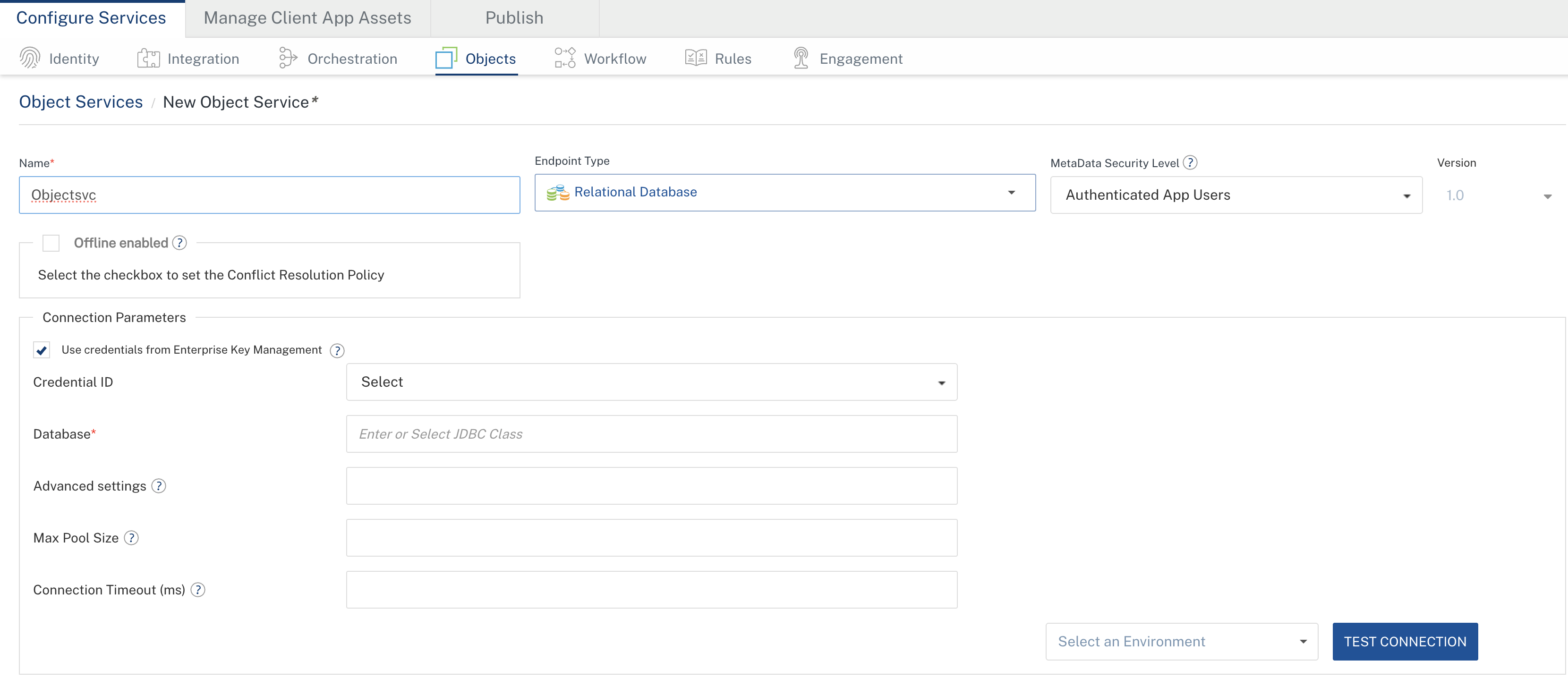
Handling Deleted Credentials in Services
When an EKM credential that is referenced by a service is deleted:
-
The service configuration displays the credential ID in red with a [DELETED] tag (e.g.,
my_db_cred [DELETED]).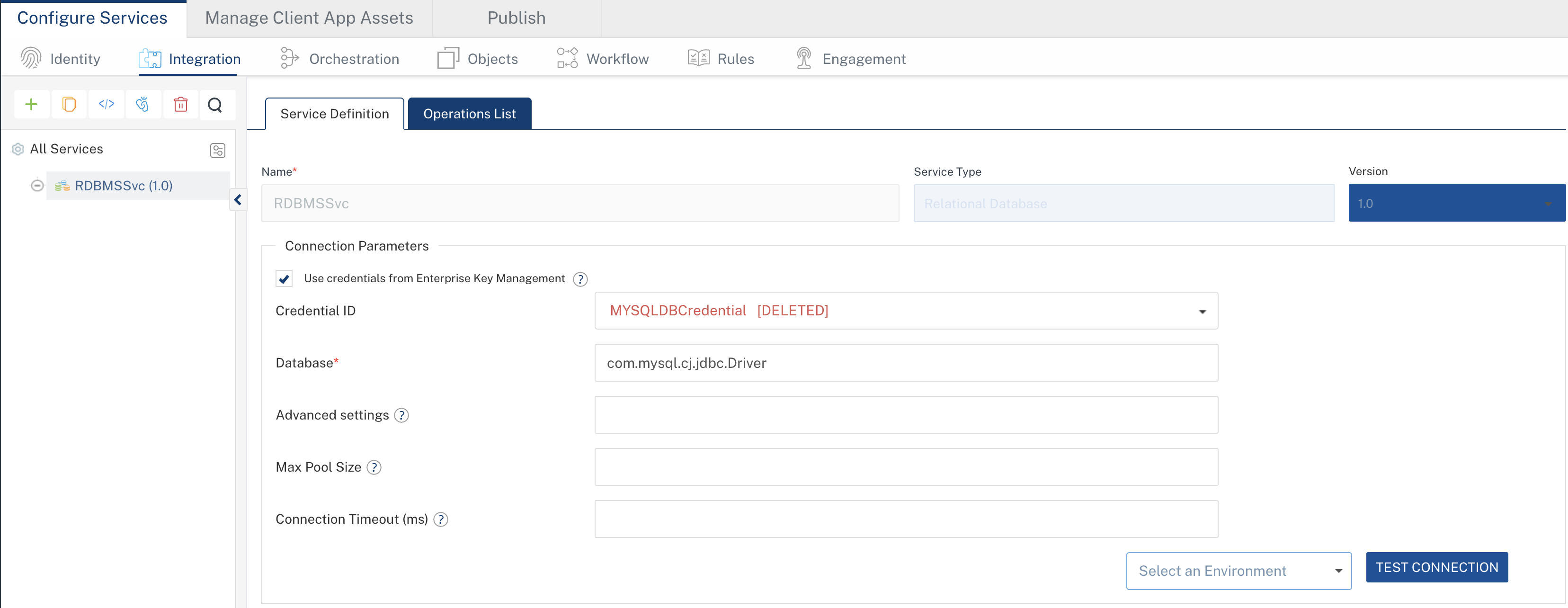
-
The service must be updated before it can be published successfully.
Resolution Steps
- Open the affected service configuration.
- In the Credential ID dropdown, select a different valid credential, OR uncheck Use credentials from Enterprise Key Management and enter credentials manually.
- Save the service configuration.
Important: Always verify that no services reference a credential before deleting it. Deleting a credential that is actively used can cause publish and runtime failures.
EKM APIs for CI/CD Automation
You can automate EKM credential management using the Foundry workspace REST APIs. These APIs help automate creating, updating, deleting, and listing credentials without using the Foundry Console.
Note: All EKM APIs are secured and require authentication via the
X-VoltMX-Authorizationheader.
Supported EKM APIs
| API | Description |
|---|---|
| Create Credential | Create a new EKM credential |
| Get All Credentials | Retrieve all credentials in the workspace |
| Get Credential IDs by Type | Retrieve credential IDs filtered by type |
| Update Credential | Update an existing credential |
| Delete Credential | Delete a credential by ID |
| Change Ownership | Transfer credential ownership to another admin |
Base URL
https://<workspace-host>/api/v1/ws/{workspaceId}/ekm
Replace <workspace-host> with your workspace URL (e.g., 100000012.workspace.sit-hclvoltmx.net for Cloud, or your on-premises hostname).
Create Credential
Endpoint:
POST https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/createCredentials
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Content-Type |
Yes | application/json |
Request Body:
{
"credentialId": "my_oauth_cred",
"credentialType": "oauth_credentials",
"description": "OAuth credential for Okta",
"credOwnerOnly": false,
"meta": "{\"client_id\":\"abc123\",\"client_secret\":\"secret456\"}"
}
Request Body Fields:
| Field | Type | Required | Description |
|---|---|---|---|
credentialId |
String | Yes | Unique identifier (max 50 chars) |
credentialType |
String | Yes | One of the supported credential types (see table below) |
description |
String | Yes | Brief description (max 80 chars) |
credOwnerOnly |
Boolean | No | If true, only the creator and Owners can edit/delete |
meta |
String | Yes | Type-specific key-value pairs (see Meta Fields table) |
Supported credentialType Values:
| Value | Credential Type |
|---|---|
oauth_credentials |
OAuth2.0 |
database_credentials |
Database |
s3_bucket_credentials |
S3 Bucket |
salesforce_credentials |
Salesforce |
username_password_credentials |
Username/Password |
awsapi_gateway_credentials |
AWS API Gateway |
redhat_pam_credentials |
Red Hat PAM |
mongodb_credentials |
MongoDB |
certificate_based_auth_credentials |
Authentication Certificate |
Meta Fields by Credential Type:
| Credential Type | Meta Fields |
|---|---|
oauth_credentials |
client_id, client_secret |
database_credentials |
dbURL, dbUserName, dbPassword |
s3_bucket_credentials |
accessKey, accessSecret, backendURL, region, bucketPath, serviceNamespace |
salesforce_credentials |
loginUrl, client_id, client_secret, username, password |
username_password_credentials |
userid, pwd |
awsapi_gateway_credentials |
AWSApiGatewayAccessKeyId, AWSApiGatewaySecretKey |
redhat_pam_credentials |
endpointUrl, username, password |
mongodb_credentials |
host, port, databaseName, username, password |
certificate_based_auth_credentials |
See Authentication Certificate Sub-Types |
Sample Response (201 Created):
{
"credentialId": "my_oauth_cred",
"credentialType": "oauth_credentials",
"workspaceId": "100000012",
"meta": "{\"client_id\":\"abc123\",\"client_secret\":\"****\"}",
"description": "OAuth credential for Okta",
"credOwnerOnly": false,
"createdBy": "admin@example.com",
"updatedBy": "admin@example.com",
"createdAt": "2026-03-31T10:00:00Z",
"updatedAt": "2026-03-31T10:00:00Z"
}
Note: Sensitive fields in the response are always masked as
****.
Validations:
credentialIdmust be unique within the workspace.credentialTypemust be a supported type.metamust contain only the allowed keys for the selected type.- Only Admin or Owner users can call this API.
Get All Credentials
Endpoint:
GET https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/getCredentials
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Sample Response (200 OK):
[
{
"credentialId": "my_oauth_cred",
"credentialType": "oauth_credentials",
"workspaceId": "100000012",
"meta": "{\"client_id\":\"abc123\",\"client_secret\":\"****\"}",
"description": "OAuth credential for Okta",
"credOwnerOnly": false,
"createdBy": "admin@example.com",
"updatedBy": "admin@example.com",
"createdAt": "2026-03-31T10:00:00Z",
"updatedAt": "2026-03-31T10:00:00Z"
}
]
Validations:
- Only Admin or Owner users can call this API.
Get Credential IDs by Type
Endpoint:
GET https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/getCredentialIDByType?credentialType={type}
Query Parameters:
| Parameter | Required | Description |
|---|---|---|
credentialType |
Yes | Filter by credential type (e.g., oauth_credentials) |
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Sample Response (200 OK):
["my_oauth_cred", "prod_oauth_cred"]
Note: This API returns only credential IDs (not full details) and is used by the Foundry Console to populate credential dropdowns. All roles (including Members/Developers) can call this API.
Update Credential
Endpoint:
PUT https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/updateCredential
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Content-Type |
Yes | application/json |
Request Body:
{
"credentialId": "my_oauth_cred",
"credentialType": "oauth_credentials",
"description": "Updated description",
"credOwnerOnly": true,
"meta": {
"client_id": "new_abc123",
"client_secret": "new_secret456"
}
}
Note:
credentialTypeandcredentialIdcannot be changed. Include them for identification.Note: To keep an existing sensitive value unchanged, pass its masked value (
****). The system will preserve the original value.
Validations:
- Only Admin or Owner users can call this API.
- If
credOwnerOnlyistrueon the credential, only the credential owner and account Owners can update it. metamust contain only allowed keys for the credential type.
Sample Response (200 OK): Same structure as Create Credential response.
Delete Credential
Endpoint:
DELETE https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/deleteCredential/{credentialID}
Path Parameters:
| Parameter | Required | Description |
|---|---|---|
credentialID |
Yes | The credential ID to delete |
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Sample Response (200 OK): Empty body on success.
Validations:
- Only Admin or Owner users can call this API.
- If
credOwnerOnlyistrueon the credential, only the credential owner and account Owners can delete it.
Important: Deleting a credential that is referenced by services will cause those services to display the credential as [DELETED]. Verify no services reference the credential before deletion.
Change Ownership
Endpoint:
PUT https://<workspace-host>/api/v1/ws/{workspaceId}/ekm/changeOwnership
Headers:
| Header | Required | Description |
|---|---|---|
X-VoltMX-Authorization |
Yes | Auth token |
Content-Type |
Yes | application/json |
Request Body:
{
"id": "my_oauth_cred",
"emailID": "newowner@example.com"
}
Request Body Fields:
| Field | Type | Required | Description |
|---|---|---|---|
id |
String | Yes | The credential ID to transfer |
emailID |
String | Yes | Email of the new owner |
Validations:
- Only Admin or Owner users can call this API.
- The new owner must be an Admin or Owner on the account.
- If
credOwnerOnlyistrue, only the current credential owner and account Owners can transfer ownership.
Sample Response (200 OK): Returns the updated credential with masked meta.
Limitations
- EKM is available only for Admin and Owner users for credential management. Members and Developers can only select credential IDs when configuring services.
- Credential types and IDs cannot be changed after creation. To change the type, delete the credential and create a new one.
- Each credential ID must be unique within an account.
- Certificate file uploads for the Authentication Certificate type are limited to 1 MB.
Notes
- All credential values are encrypted at rest in the Foundry database using the WaaS master encryption key.
- Sensitive fields (passwords, secrets, access keys) are displayed as
****in the Foundry Console and API responses. - EKM is an account-level feature. Credentials created in one account are not accessible from other accounts.
- When editing a credential, if you leave a masked sensitive field unchanged, the original value is preserved.
- Ownership transfer requires the new owner to be an Admin or Owner on the account.
- When the Limit update permission to credential owner option is enabled, only the credential creator (and account Owners) can edit or delete that credential.
Frequently Asked Questions
Q: Who can create and manage EKM credentials?
Only users with Admin or Owner roles can create, update, delete, and manage credentials. Developers and Members can only reference credential IDs in service configurations.
Q: Can developers see the actual credential values?
No. Credential values are always masked (****) in the Console and API responses. Developers can only see and select credential IDs.
Q: What happens if I delete a credential that is used by a service?
The service configuration will display the deleted credential ID in red with a [DELETED] tag. The service cannot be published until you select a valid credential or provide credentials manually.
Q: Can I use the same credential in multiple services?
Yes. A single EKM credential can be referenced by multiple Identity, Integration, and Object services.
Q: Is EKM backward compatible?
Yes. Existing services that use directly configured credentials continue to work as before. EKM is an opt-in feature — developers choose to enable it per service by checking the Use credentials from Enterprise Key Management checkbox.
Q: What is the "Limit update permission to credential owner" option?
When enabled, only the user who created the credential (and account Owners) can edit or delete that credential. Other Admin users cannot modify it.
Q: How are credentials secured?
Credentials are encrypted at rest in the database. Sensitive fields are masked in all API responses and Console views. Credential resolution is done securely at publish time, and secrets are never logged.
Q: Can I change the credential type after creation?
No. The credential type and ID are immutable after creation. To change the type, delete the existing credential and create a new one with the desired type.
Q: Does EKM support Test Login for Identity services?
Yes. When testing an OAuth2 identity provider that uses EKM credentials, the system securely resolves the credential values before performing the test authentication.