Adding an application in Azure AD for SSO with Connections
Part of setting up single sign-on with OIDC involves registering an application in Microsoft Azure Active Directory.
Procedure
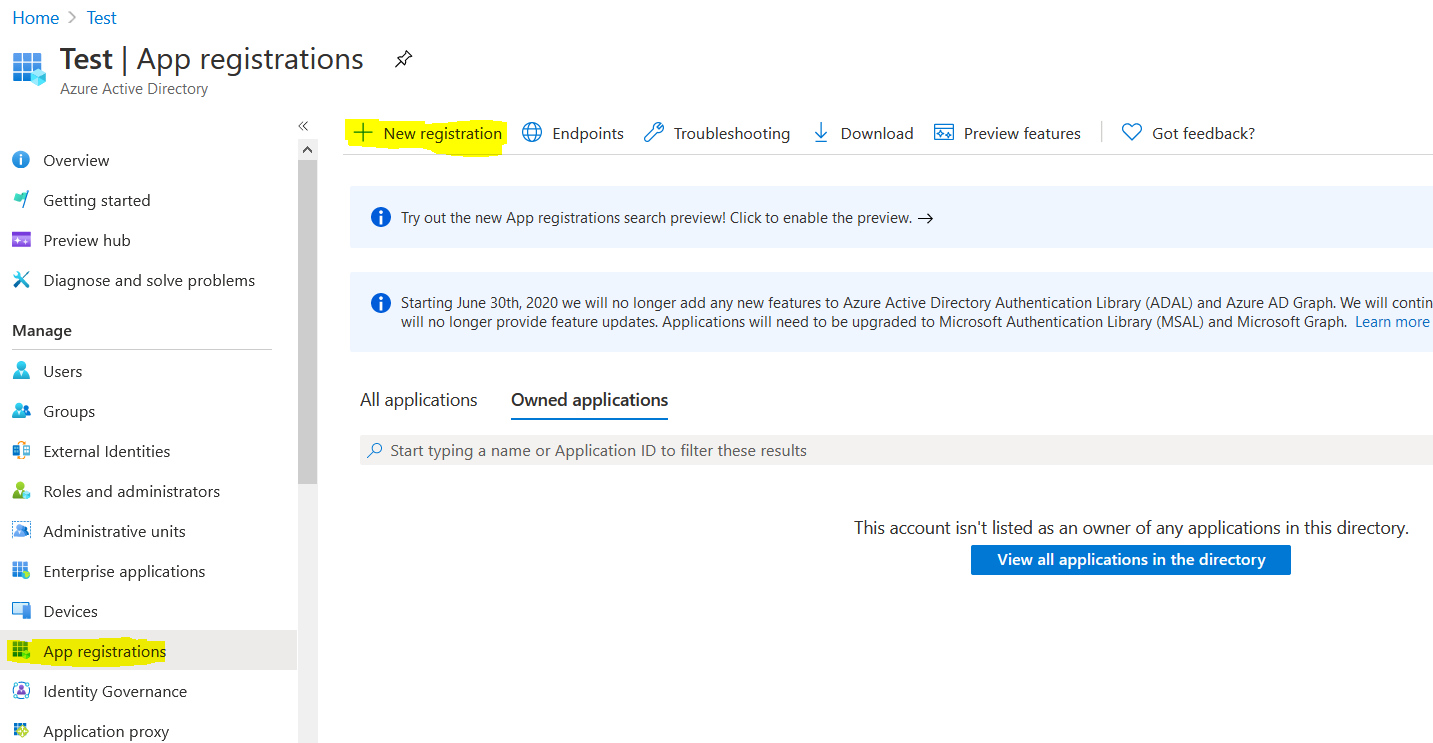
- Login to the Azure portal to add the Connections application to Azure, at https://portal.azure.com.
-
Under Manage, click App Registrations and then click
New registration in the action bar.
-
Provide the following details for the application you are registering:
- Name
- Supported account type = Multitenant
- Redirect URI (you fill this in after configuring the WebSphere TAI)
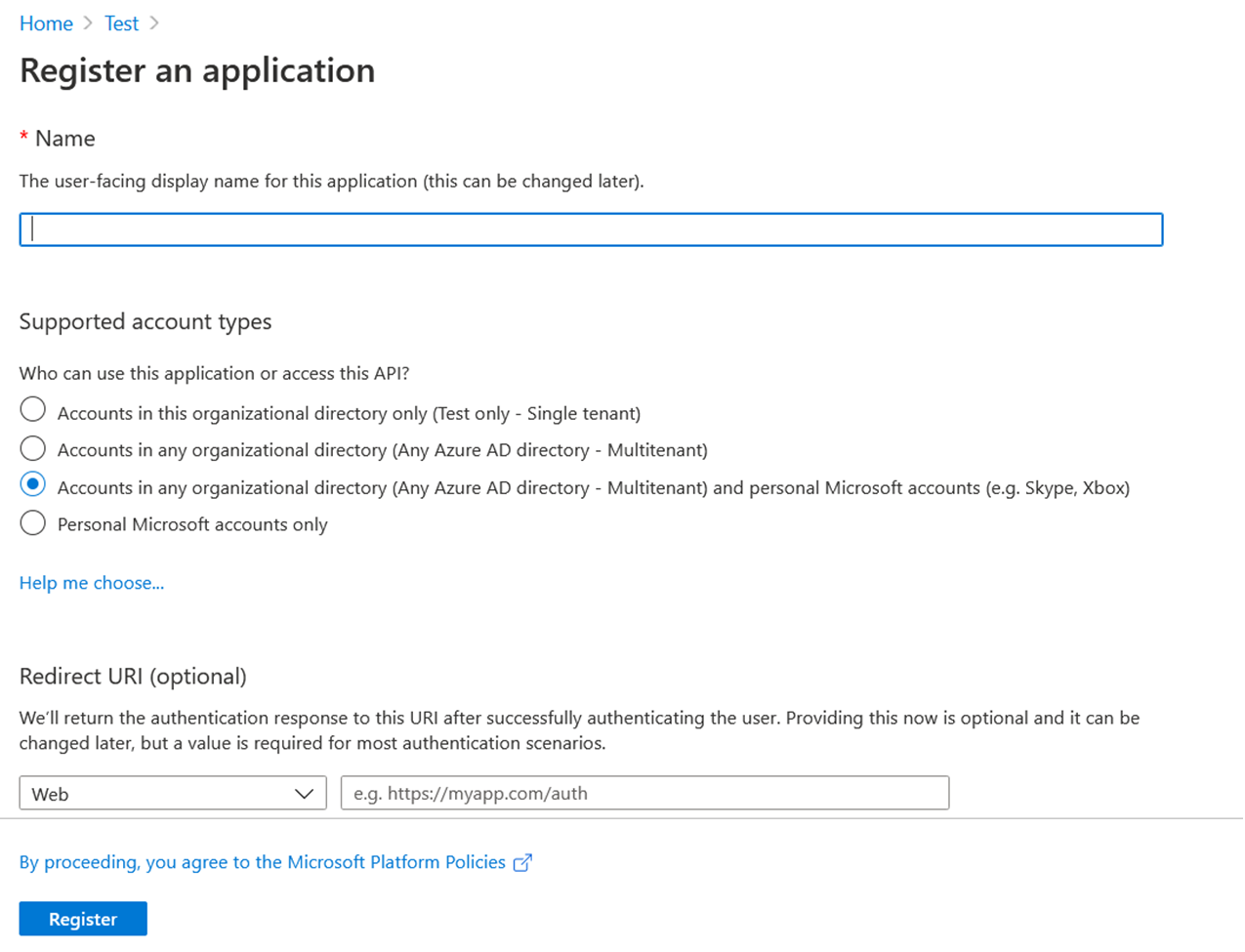
- Tips
- Provide the name of your application.
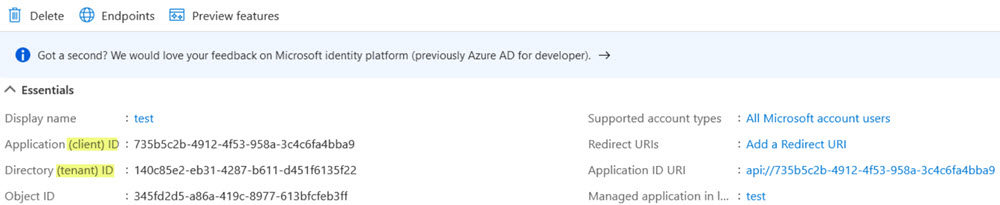
Important:Values are generated for the client ID and tenant ID. Copy the values from your screen, along with the client secret that you will generated in step 4, for use later when configuring WebSphere.
-
Create a client secret: Navigate to .
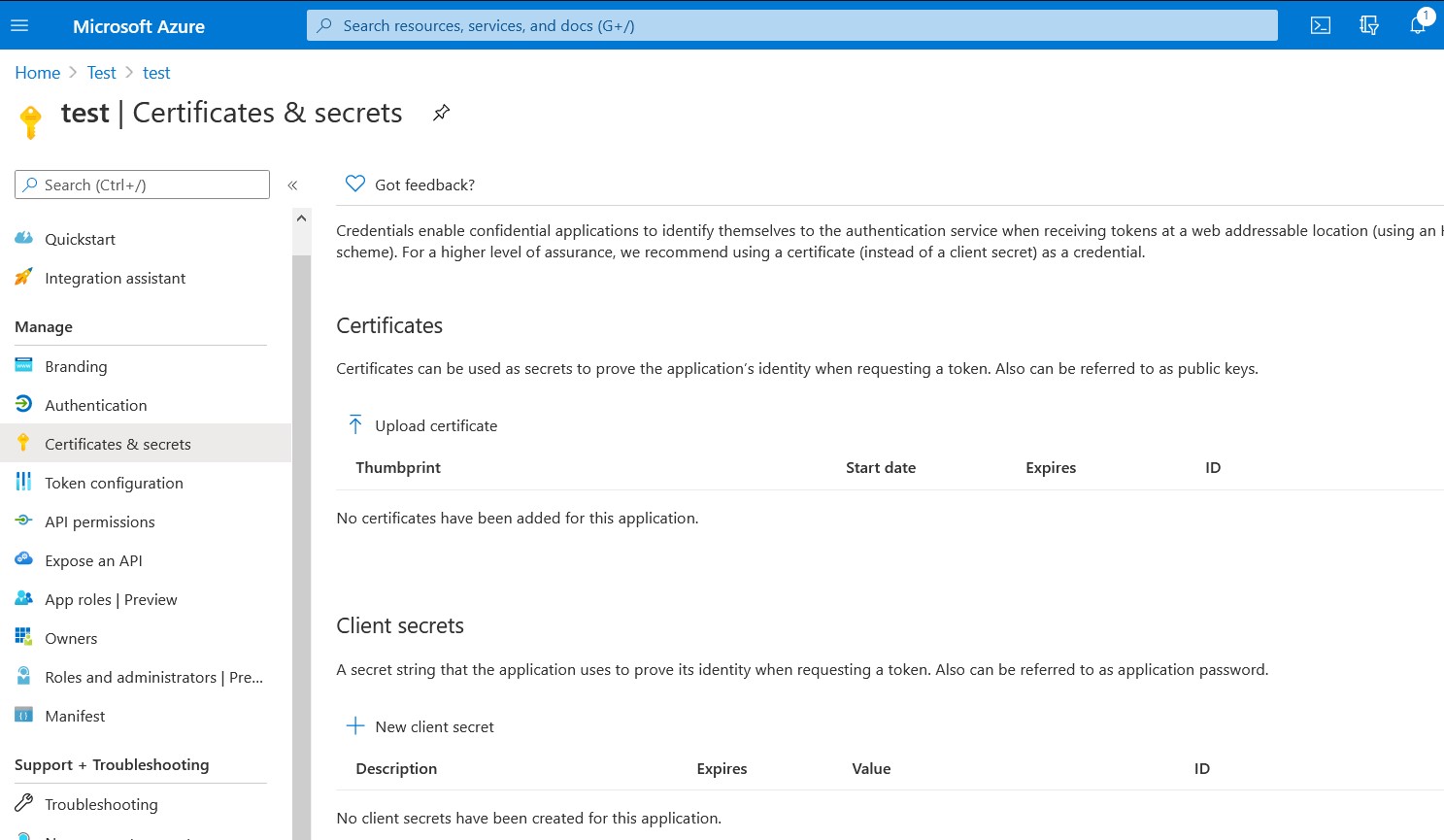
Note: Remember to copy the secret for use later when configuring WebSphere. -
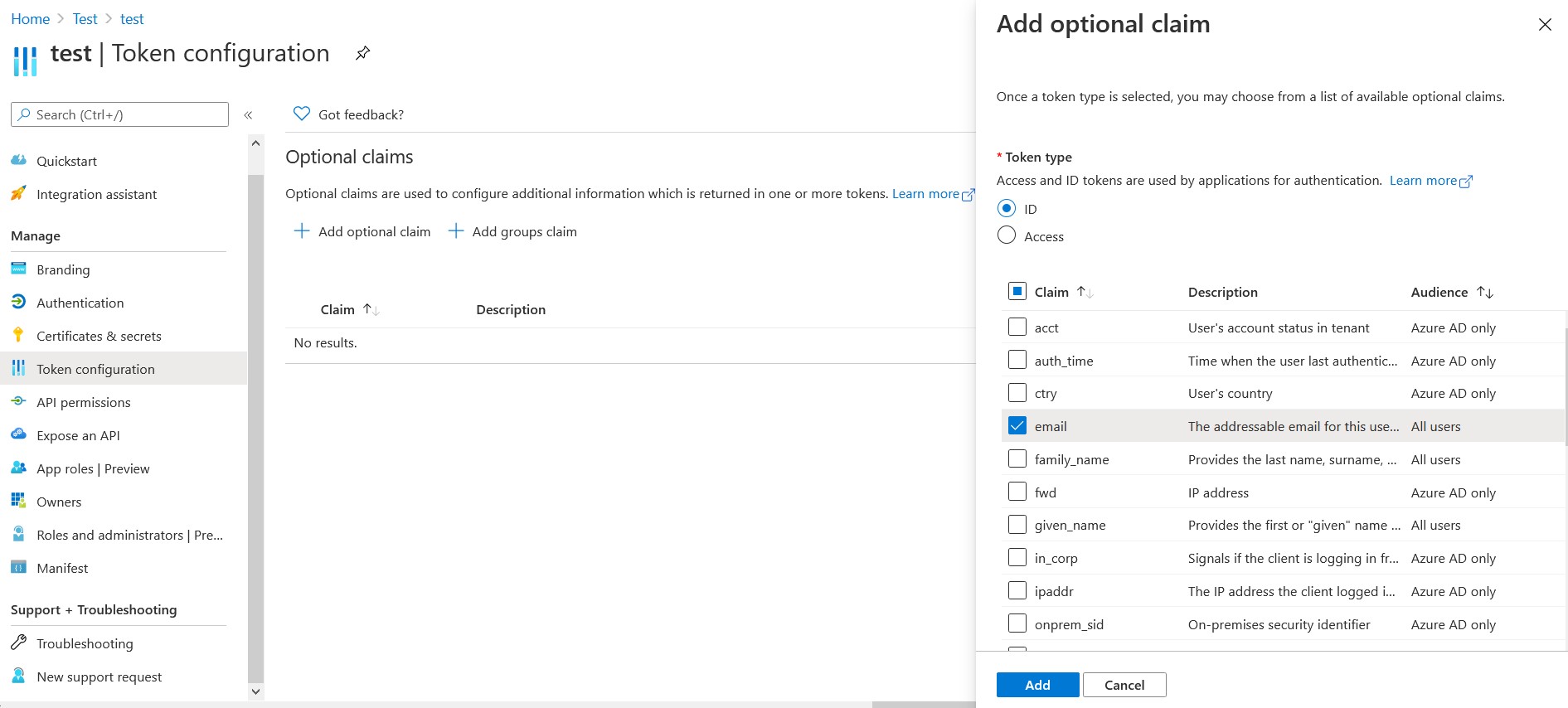
Provide information on token configuration:
- For the ID token type, navigate to . Select email and then click Add.
- Repeat for the access token: Navigate to , and select Access. Now select email and click Add.
-
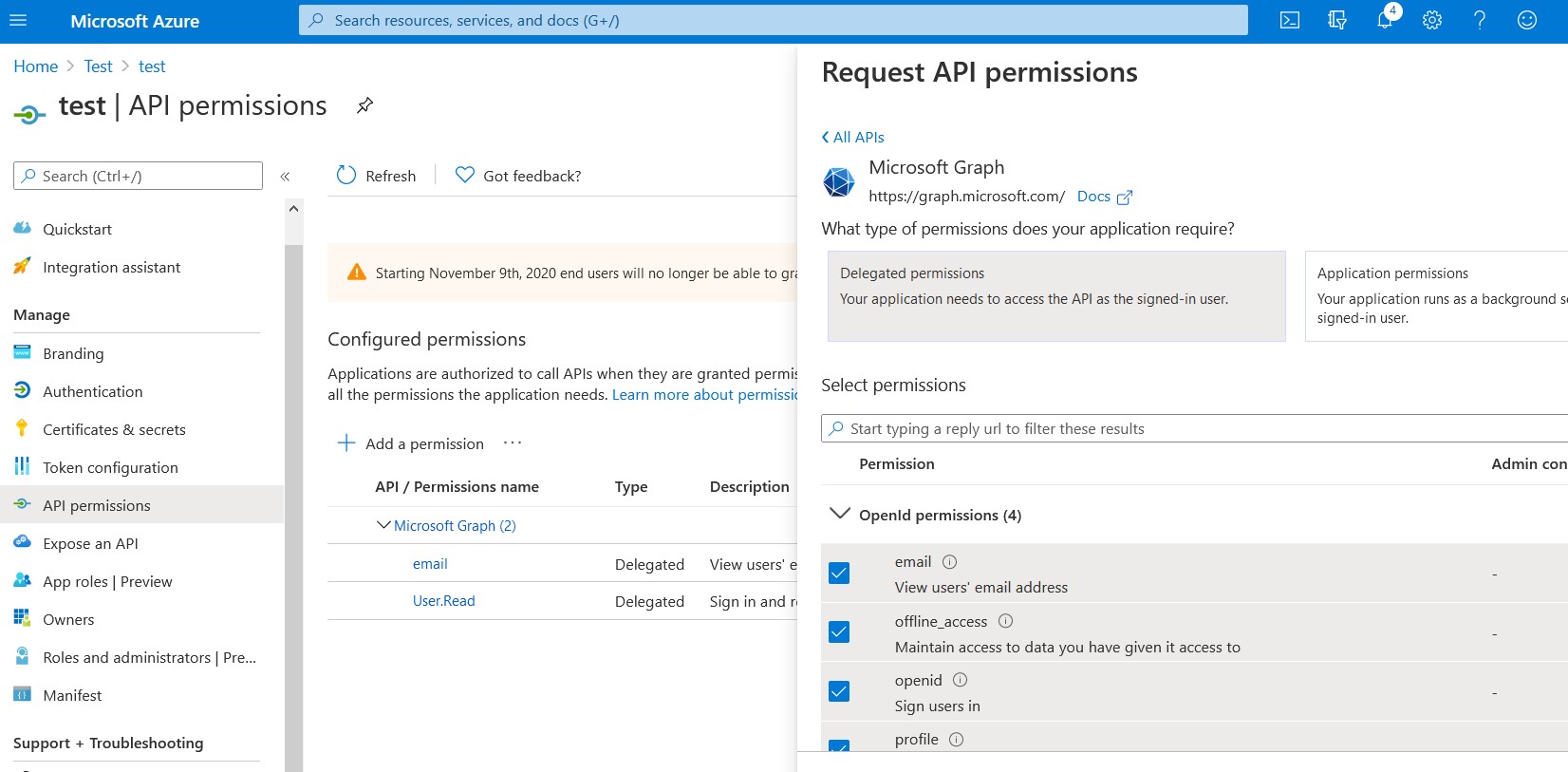
Add permissions by navigating to and completing the following actions:
-
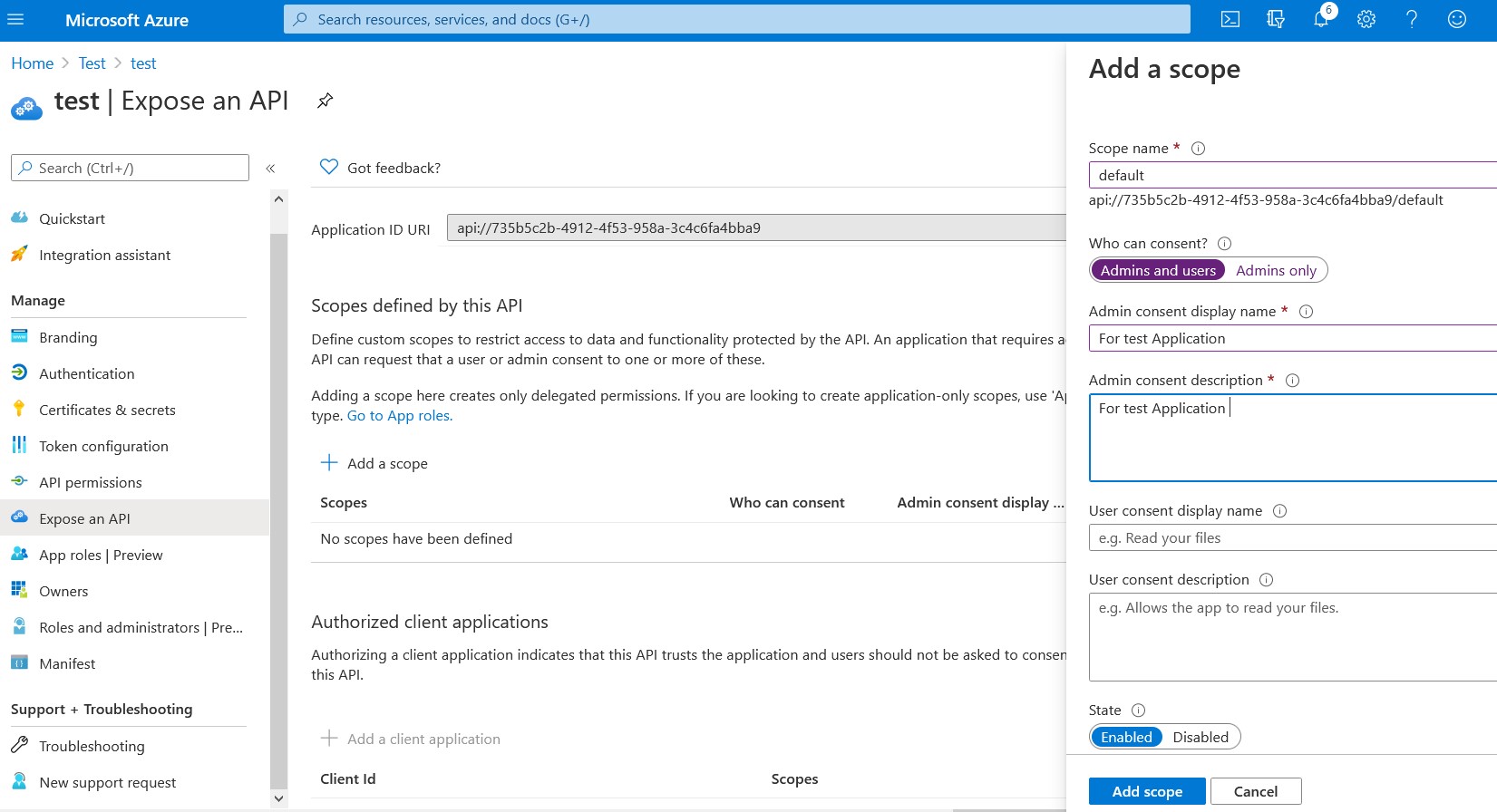
Expose an API by defining a scope to ensure that the correct Oauth access token
is used:
-
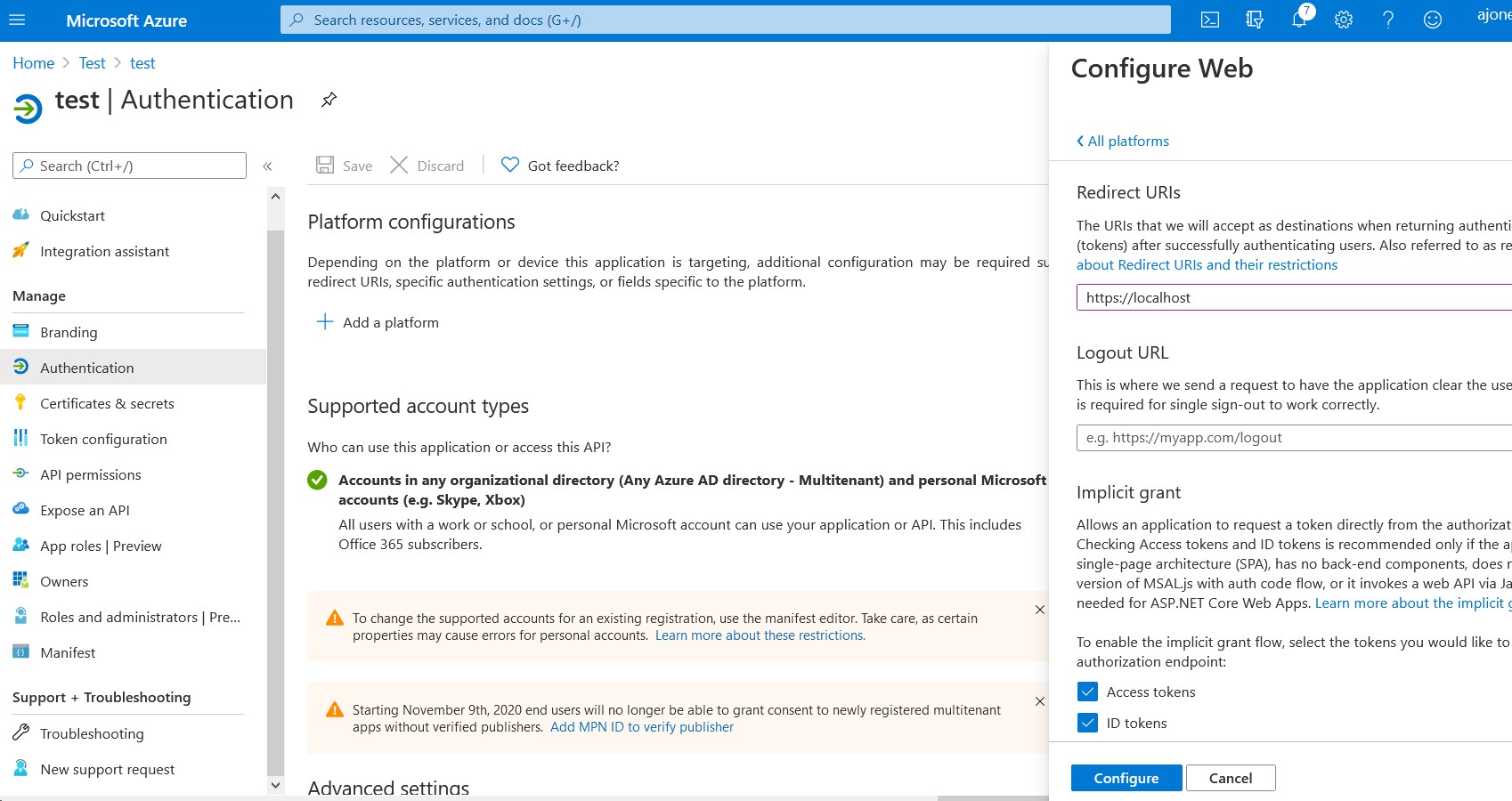
Add a redirect URI. (You'll do this once you've completed the next procedure in
this documentation.)
https://<Hostname>/<context_root> /<provider_1.identifier>where- Hostname is the hostname of the server on which HCL Connections is running
Context_rootis obtained from the table at this (WebSphere) location:provider_1.identifieris the value of the OIDC TAI property from WebSphere
- For troubleshooting, you can validate configuration values by navigating to to view the manifest file.
What to do next
Update WebSphere to support Azure AD OIDC authentication for Connections