System Architecture
The system architecture of Application Control.
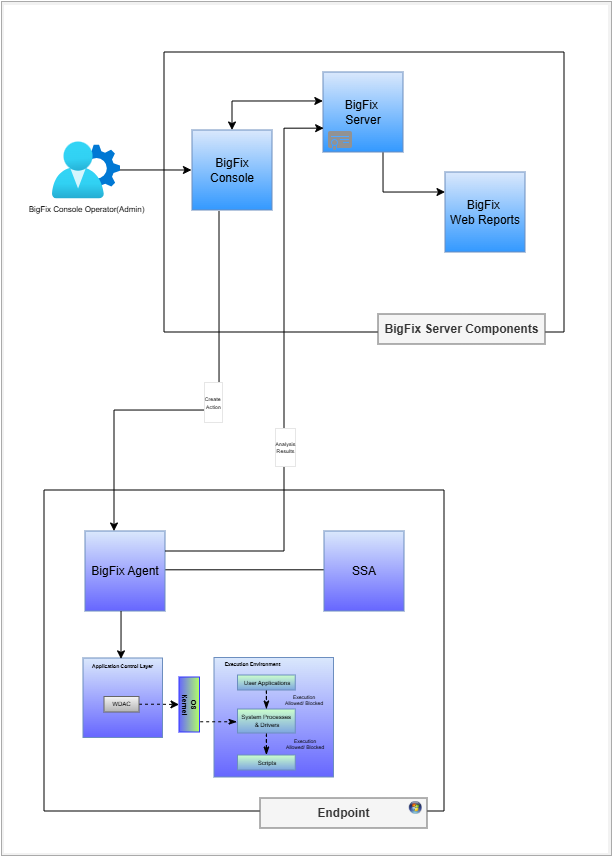
The above diagram shows how the BigFix Server components interact with BigFix endpoints and other components.
The system architecture diagram illustrates the interaction between BigFix Server components and BigFix endpoints. This visual representation aids in understanding the structure and functionality of the BigFix Application Control system.
-
- BigFix Server Components
- Application Control mainly utilizes the following three BigFix® Server Components:
-
- BigFix® Core Server
- This is the central processing component for this solution. It manages all communications with the BigFix clients (agents), distributes content (like Fixlets, tasks, and analysis), and enforces policies.
-
- BigFix® Console
- The console is the primary administrative interface for BigFix Application Control. It is a key part of the server-side infrastructure used to manage all aspects of the environment, including creating content and deploying actions. All BigFix Console integrations will be in the External Site.
-
- BigFix® Web Reports
- It provides a web-based interface for reporting
and data visualization. The BigFix Agent on the
endpoint runs an analysis and sends the result to
the BigFix server. Below administrative report(s)
that are shown for Application Control:
- Effective Policy on Endpoint
-
-
- Endpoints
- On the endpoints the BigFix agent is installed which communicates with Application Control Layer to enforce allowlisting or blocklisting of applications using kernel-based WDAC.
WDAC Enforcement Model: The Application Control policy is authored in XML, then compiled to binary, and then is digitally signed. The digitally signed certificate is then deployed to <EFI System Partition>\EFI\Microsoft\Boot\CiPolicies\Active\. The OS kernel validates the policy and only the allowlisted applications are allowed to execute.